![Computer Security: [Pen|Pan|Pant]testing](https://nextai.talc.online/wp-content/uploads/2026/03/Picture201_0-1.png)
Computer Security: [Pen|Pan|Pant]testing
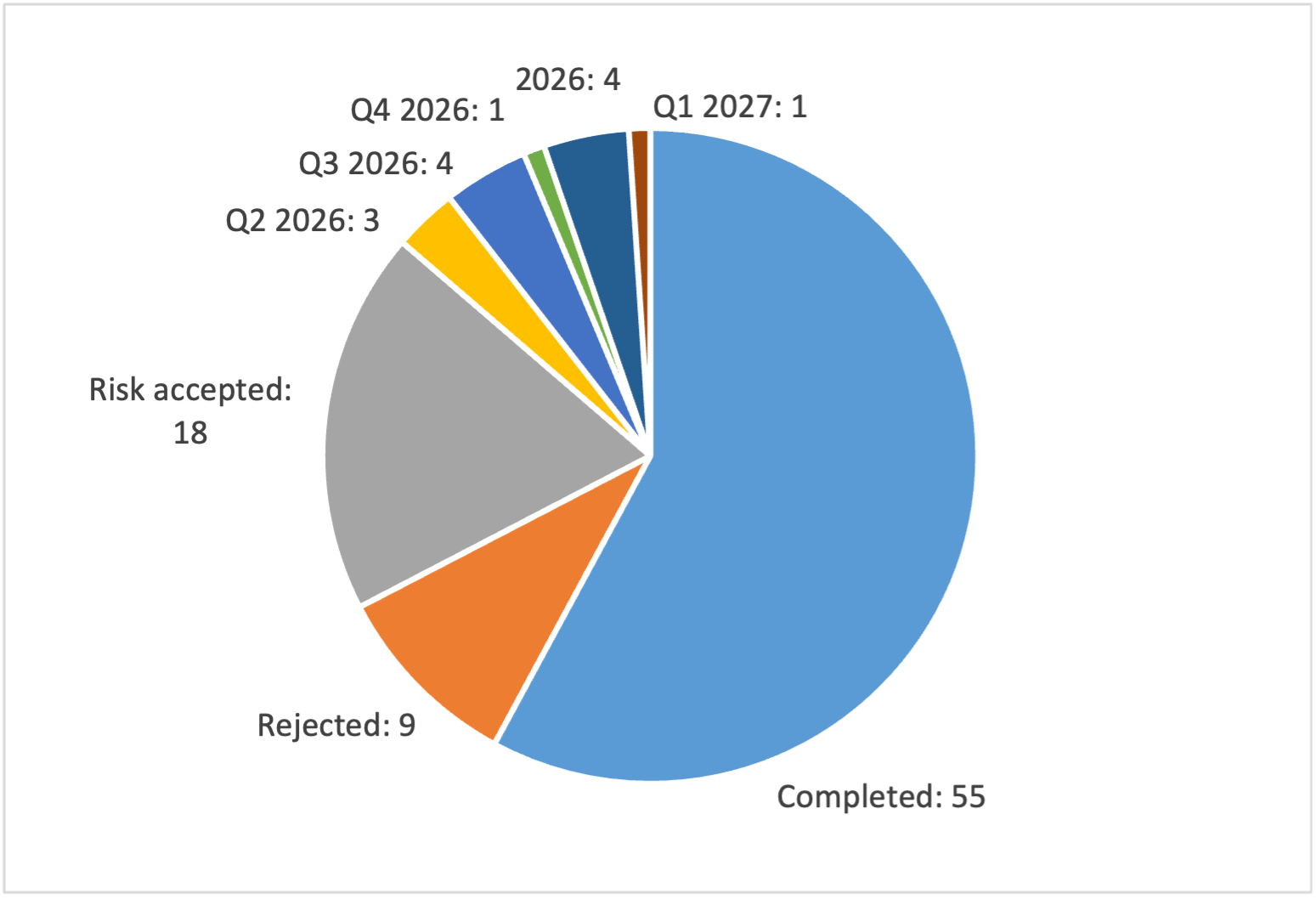
Following the successful conclusion of the 2023 cybersecurity audit, 2026 will see another series of vulnerability assessments, penetration tests (“pentests”) and cybersecurity reviews. While some are mandatory and conducted regularly, like those initiated when CERN buys new IT equipment, new software, or new hardware with an IT component, when CERN launches new projects encompassing information technology or when critical CERN computing services undergo a transition or migration to a newer major version, others are rather ad hoc and triggered at the initiative of the Computer Security Office. Here’s a short summary of what’s coming up next.
While the 2023 cybersecurity audit was formally and officially concluded by the CERN audit team at the end of 2025, some of its recommendations could only be scheduled for implementation in 2026 as either sophisticated preparations were needed or their deployment would heavily impact accelerator and experiment operations and therefore had to wait for LS3. Hence, this year will also see the technical conclusion of those remaining audit points, e.g. the change towards using 15-character passwords, the roll-out of 2-factor authentication to virtual machines used for accelerator software development, the newly encrypted CERN Wi-Fi (based on WPA3), the technical enforcement of CERN’s Computing Rules and the deployment of dedicated firewall protections for CERN’s Technical Network and, in 2027, the Campus network. So there is still some heavy lifting ahead.
And there is more to come: at the end of 2025, the Computer Security Office contracted a penetration test of CERN’s Active Directory (AD) by an external company. Working like real attackers would, their experts were supposed to identify potential weaknesses and vulnerabilities in CERN’s AD which might allow an attacker to take over CERN’s computing infrastructure. And it comes as no surprise that they found a series of areas for improvement, so 2026 will see some modifications to CERN’s AD set-up and its LDAP configuration (like the extension of the usage of secure protocols like LDAPS, introduction of SMB signing, hardening of UNC paths, removal of insecure (encryption) protocols, and the change of some internal passwords). While many of these changes will happen behind the scenes, others might have some impact on CERN in general. However, as usual, the corresponding interventions will be announced well in advance.
In addition, in order to learn more about password hygiene at CERN and to complement the ongoing change from 8-character passwords with a certain complexity of symbols, numbers and upper/lowercase letters towards 15-character passwords (minimum), the Computer Security Office has invited a specialised company to come on site and try to brute-force and crack the passwords of CERN centrally managed primary, secondary and service accounts in a privacy-preserving manner. Owners of accounts with weak passwords will be informed and asked to improve their choice.
Also on the cards is a full-fledged vulnerability scan of thousands of internet-facing, public websites hosted at CERN (and not protected by the CERN Single Sign-On) as well as hundreds of servers opened towards the internet in order to identify weaknesses, misconfigurations and vulnerabilities. The corresponding tender is currently out, and the work is expected to be conducted during summer 2026 (and the findings fixed right afterwards). Once more, owners of websites or servers found to need improvement will be contacted directly. Already, here, a thank you for quickly addressing any issues!
And, finally, on 1 April, the Computer Security Office will invite all interested parties to conduct a series of pen-, pan- and panttesting offered in CERN’s Restaurant 2… Feel free to join!
Do you want to learn more about computer security incidents and issues at CERN? Follow our Monthly Report. For further information, questions or help, check our website or contact us at Computer.Security@cern.ch.
ehatters
